SECURITY. Determines how WebFOCUS connects to the Reporting Server. The following are possible
SECURITY values:
Default. Is the initial value
for new nodes and represents the traditional behavior, where the
odin.cfg file does not contain a SECURITY keyword. In this case, WebFOCUS makes an explicit connection to the Reporting Server
with the user ID and password it has available for the request.
HTTP Basic. Configures WebFOCUS to
extract the user ID and password from the Authorization header. These
credentials are then used to make an explicit connection to the
Reporting Server. You should only select this option when your web
tier is performing Basic Authentication.
To verify that the
Authorization header is available to WebFOCUS, expand the Diagnostics node
in the Administrative Console and select HTTP Request
Info.
Kerberos. Configures WebFOCUS to
pass the Kerberos ticket for the user to the Reporting Server. This option
enables an end-to-end single sign on solution from the desktop to WebFOCUS, from WebFOCUS to the Reporting Server,
and from the Reporting Server to supported relational DBMS systems.
When using this option, the Reporting Server must run in security
OPSYS mode. Kerberos must be specified in the odin.cfg file.
SAP Ticket. Enables
customers using Open Portal Services in SAP Enterprise Portal to
achieve single sign on through WebFOCUS to a Reporting Server configured
with the Data Adapter for SAP. WebFOCUS passes along the MYSAPSSO
cookie of the user, created on SAP Enterprise Portal, to the Reporting
Server. The Reporting Server validates it using the SAP security
API.
Service Account. Allows
you to specify a user ID and password to be used for all connections
to the Reporting Server.
The service
account credentials are encrypted and stored in the SECURITY keyword
of the odin.cfg file. When defined, the service account overrides
any other credentials that may be presented to WebFOCUS for this Reporting Server
node, and all users connect to the Reporting Server using the same
credentials. This approach does not make it possible to identify
which user is running a given request on the Reporting Server in
Managed Reporting deployments, and therefore, is not recommended
for them.
Trusted. Allows you to connect to the Reporting
Server with only a user ID. This option is useful when no password
is available for the user, and controls can be placed on the server
to ensure that connections from unauthorized clients are rejected.
For example, employing the Reporting Server RESTRICT_TO_IP setting
or configuring a network firewall so that only a particular client
can connect to the server.
Note: To complete the configuration
of a trusted connection, you must enable the Reporting Server to
accept trusted connections. Step 10 instructs you on how to configure
the Reporting Server once you have completed configuring the WebFOCUS
Client.
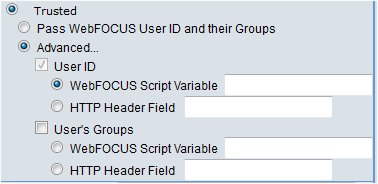
When you select Trusted,
the Pass WebFOCUS User ID and their Groups and Advanced options
become available, as shown in the following image.
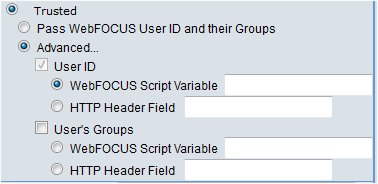
If
you select Advanced, you can enter the script variable
and web server HTTP variable settings for User ID and User’s Groups.
You can also specify the following optional parameters:
-
x
SECURITY OBJECT. For
any security option, an administrator can specify one or more HTTP
header names and/or cookie names as follows:
-
COOKIE. Specify
each HTTP cookie name separated by a comma (,). For example:
cookie_name1, cookie_name2
-
HEADER. Specify
each HTTP header name separated by a comma (,). For example:
header_name1, header_name2
Note: HTTP
cookie and header names must not contain commas (,) or colons (:),
since these are reserved delimiters.
REMOTE_USER is not a
valid value in the HEADER input box, since it is a special type
of HTTP header variable and its contents will not be sent to the
Reporting Server. Instead, specify the WF_REMOTE_USER variable.
-
HTTP_SSL. Enables
encrypted communication between the client and the Reporting Server
HTTP listener. This option must be selected if the HTTP listener
of the Reporting Server is configured to use SSL.
If you are
using a self-signed certificate to enable HTTPS communication with
a Reporting Server, the certificate must be configured in the Java
environment in which the WebFOCUS Client is installed. This enables
HTTPS communication between the Reporting Server and the following
WebFOCUS Client tools:
- Administration Console.
-
Developer
Studio metadata tools,
such as the Synonym Editor and Create Synonym tool.
-
x
COMPRESSION. Turns
on data compression. Acceptable values are 0 (off) and 1 (on).
The default value is 0.
-
x
ENCRYPTION. Sets
data encryption ability and the cryptography symmetric method used.
Select one of the following options
from the drop-down list:
-
0. Off
-
AES. Advanced
Encryption Standard. The AES selections are in the format
CIPHER(x)(-MODE)
where:
- CIPHER
Is AES128, AES192, AES256.
- x
Is optional and defines an RSA key length of 1024 bits.
- MODE
Is optional and is either Electronic Code Book (ECB) or Cipher
Block Chaining (CBC).
For example, AES256x-CBC is the AES
cipher, with 1024-bit RSA keys, and CBC mode. If the RSA or mode
is not specified, then the default values are used. The RSA default
value is 512 bits. The mode default value is ECB.
-
IBCRYPT. User-defined
IBCRYPT DLL is loaded.
-
x
CONNECT_LIMIT. Specifies
the number of seconds the client holds the pending connection. This
is useful in a cluster deployment to avoid a lengthy delay of failover
response. Other possible values are 0 (no wait) and -1 (infinite
wait). The default value is -1.
-
x
MAXWAIT. Specifies the time,
in seconds, the client waits before timeout. You can optionally
specify different return times for the first row and other rows.
A single number indicates the return time is valid for any row.
If two numbers are separated by a comma, the first number specifies
the return time for the first row and the second number specifies
the return time for the subsequent rows. The default value is -1,
which indicates an infinite wait time.
-
x
DESCRIPTION. Description
for the Reporting Server node. This description displays to end
users.
Because you specified Client in step 4, proceed
to step 9 (and skip step 7, which is used when Cluster is specified).
 icon
on the Object Explorer toolbar.
icon
on the Object Explorer toolbar.